If you are involved in vulnerability research, reverse engineering or penetration testing, I suggest to try out the Python programming language. It has a rich set of useful libraries and programs. This GitHub project lists some of them.
See the list of Python tools
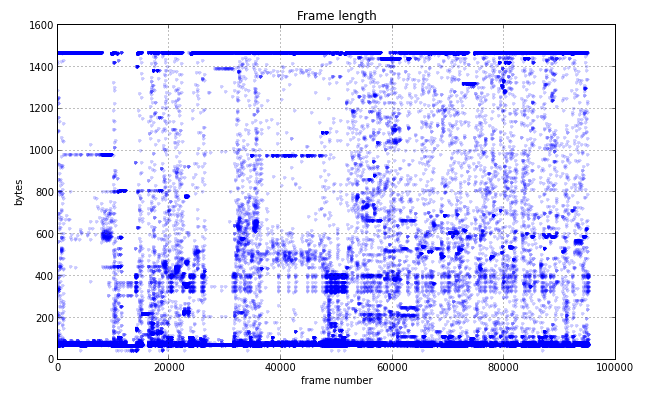
Scapy is really awesome packet capture and construction tool by Philippe Biondi, written in Python.
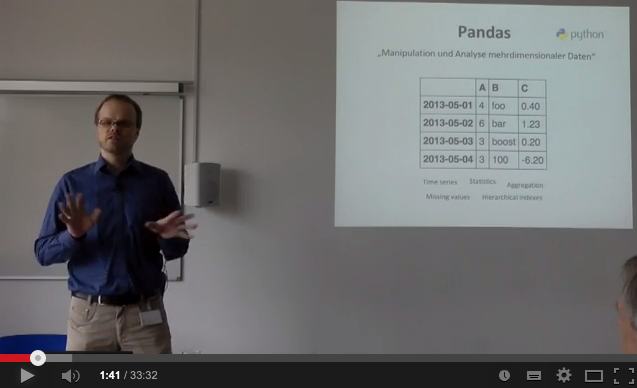
From 2007 to 2010 I severely improved the initial Windows port, wrote the Windows installation guide and integrated the existing docs into a Sphinx-based Scapy manual (PDF). Here you'll find a Windows installer for libdnet and Python 2.7 (dnet-1.12.win.32-py2.7.exe) and slides for a talk (PDF) that I gave at the PyCologne Python user group.
Scapy homepage on GitHub
I have analysed the fingerprint visualization algorithm that was introduced in OpenSSH 5.1 and wrote a short paper about it (together with Tobias Limmer and Alexander von Gernler, who had the idea for the algorithm and did the original OpenSSH implementation): The drunken bishop: An analysis of the OpenSSH fingerprint visualization algorithm (PDF).
Try the web application
Having created several bootable Windows CD-ROMs with Bart's PE Builder, I thought how nice it would be if I could use some of the plugins on running systems (i.e. without having to reboot). So in spring 2004 I started searching the Internet for useful utilities that can be run directly from CD-ROM. The resulting list is quite large, but not updated anymore.
See the list of tools on GitHub
Tempest for Eliza is a progam that makes your computer monitor send out special radio signals so that
you can then hear computer generated music in your radio. The original
software runs under Linux and the X-Window System. For demonstration purposes
I have developped a bootable CD-ROM called Tempest Showroom that includes everything in order to run Tempest for Eliza on every PC.
Find out more and download the ISO
In May 2004 I found several security holes in eSeSIX's Thintune computers. I wrote an advisory and published it on the Bugtraq mailing list. The Common Vulnerabilities and Exposures project has given the identifiers CVE-2004-2048, CVE-2004-2049, CVE-2004-2050, CVE-2004-51 and CVE-2004-2052 to these vulnerabilities.
See the CVE-2004-2048 entry
Since the early 1990ies I have been composing music.